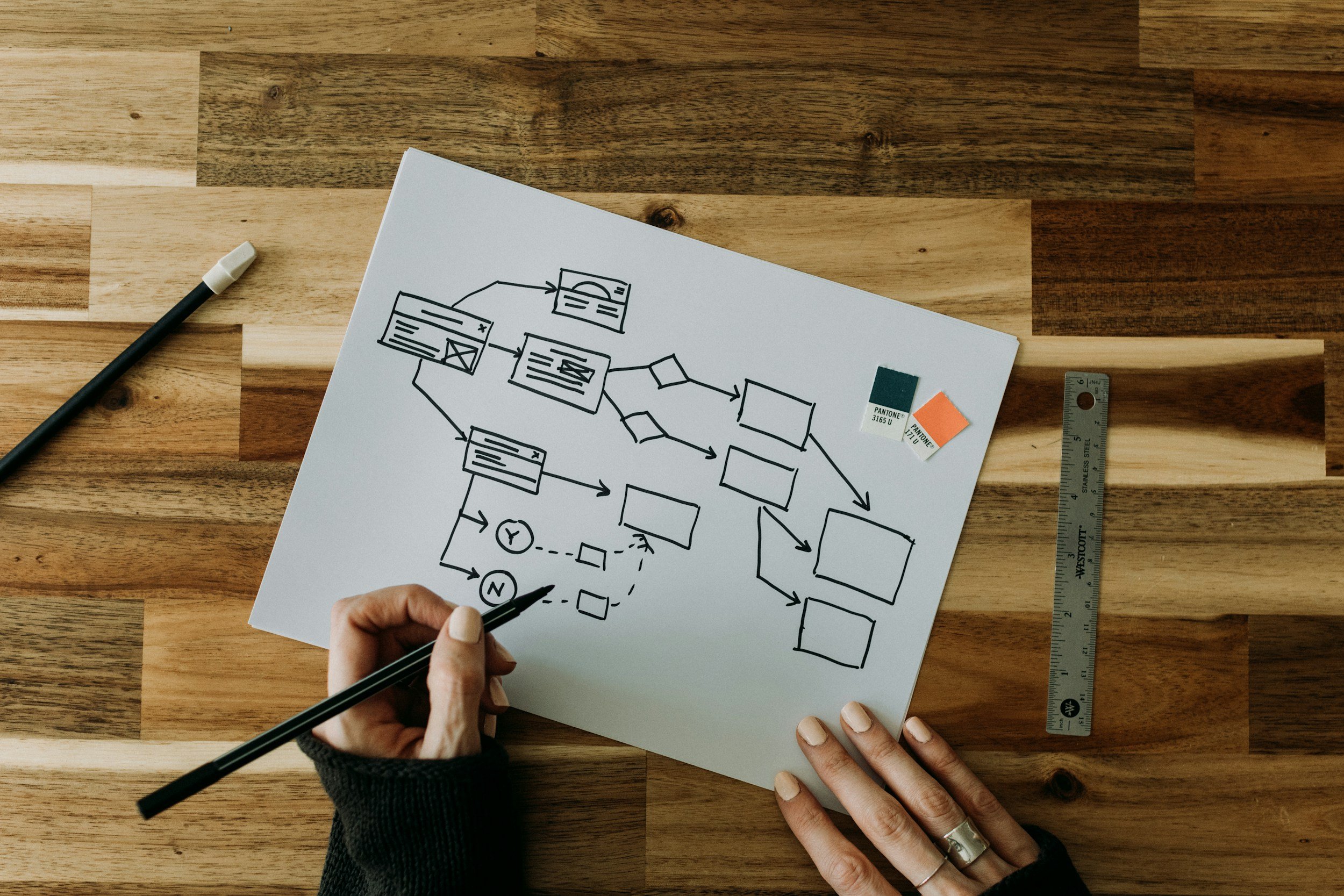
Vendor Risk Management for SaaS Companies: The SOC 2 Control Most Teams Ignore Until It's Too Late
Vendor risk management is the SOC 2 control most SaaS teams underestimate. Here's what CC9.2 actually requires, where evidence breaks down, and how to build a program that holds up under audit scrutiny.
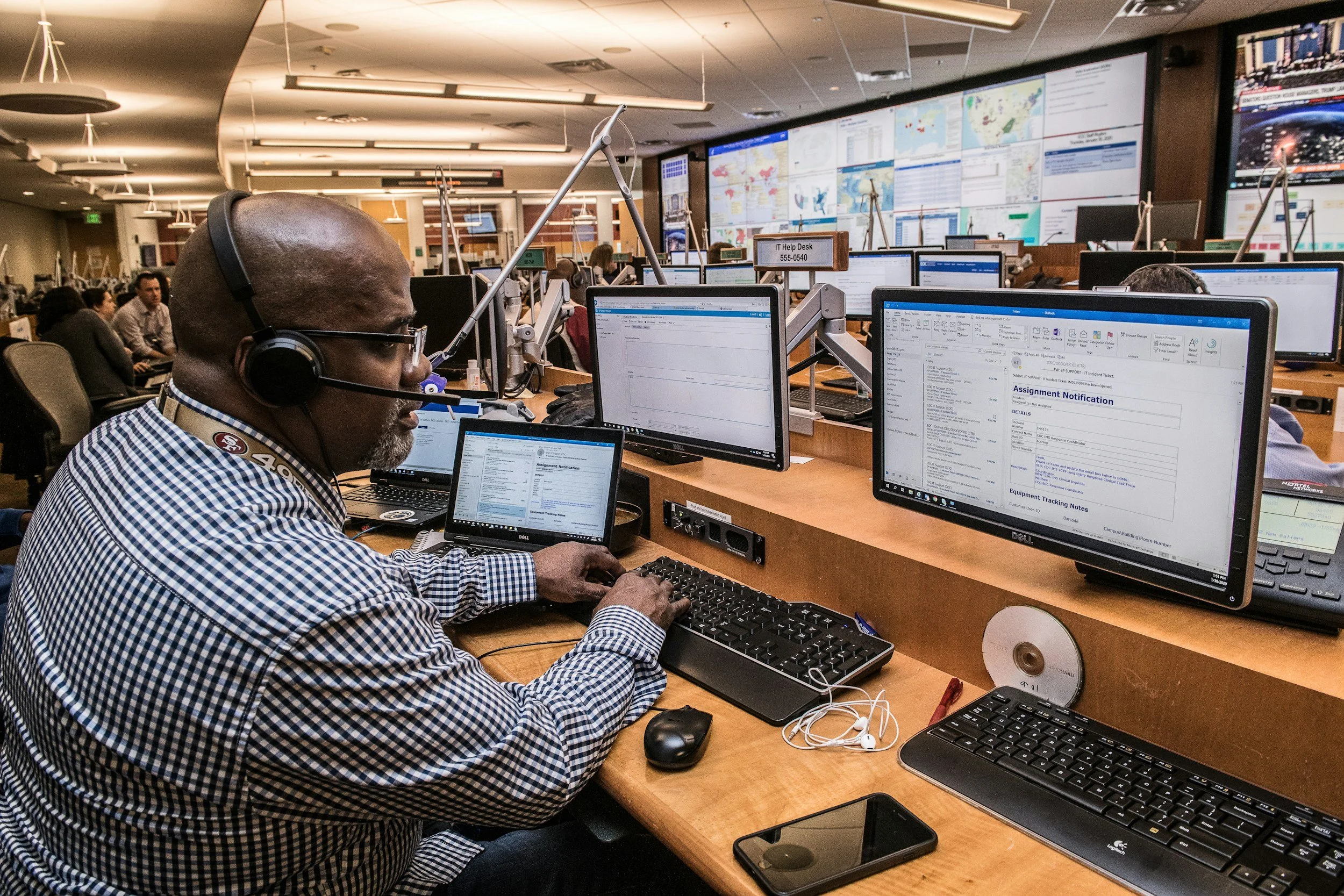
What a Tabletop Exercise Should Look Like, Include, and Why Auditors Care Whether You've Run One
Tabletop exercises are required by multiple compliance frameworks and consistently underprepared. Here's what a real tabletop should include, how to run one, and why auditors care whether you've done it.
What a CMMC System Security Plan Actually Needs to Contain (And What Assessors Flag as Incomplete)
Your System Security Plan is the foundation of your CMMC assessment. Most SSPs submitted by defense contractors are incomplete. Here's what assessors flag and what a complete SSP actually needs.
What Is a SOC 2 System Description and Why Getting It Wrong Kills Your Audit
The SOC 2 system description is the foundation of your audit report — and one of the most misunderstood deliverables in the process. Here's what it needs to contain and where first-timers go wrong.
The 3 Reasons Midwest Businesses Fail Their First Audit (and How to Avoid the "Compliance Gap")
Are you audit-ready or just 'IT-secure'? Discover the 3 most common reasons Midwest firms fail compliance audits and how to use the 'Compliance Trifecta' to pass with confidence in 2026.