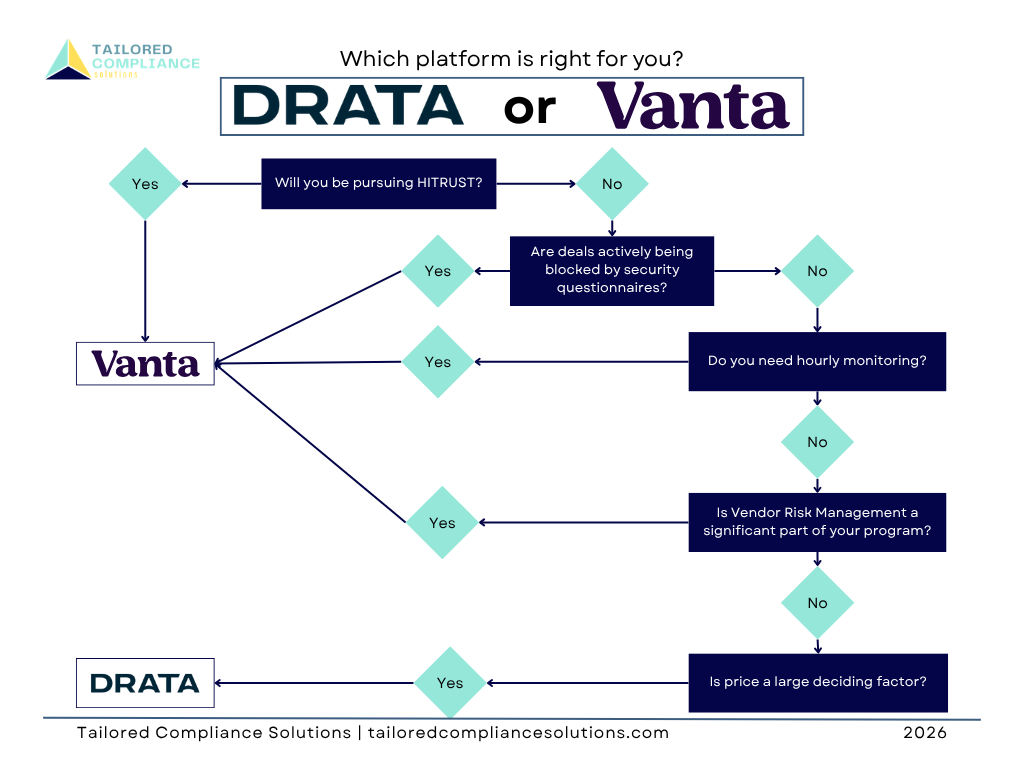
How to Choose SOC 2 Compliance Software for a SaaS Startup: Vanta vs Drata
Vanta vs Drata for SaaS? Both produce equivalent SOC 2 outcomes. The right choice depends on your specific situation. Here's the honest decision framework.
Vendor Risk Management for SaaS Companies: The SOC 2 Control Most Teams Ignore Until It's Too Late
Vendor risk management is the SOC 2 control most SaaS teams underestimate. Here's what CC9.2 actually requires, where evidence breaks down, and how to build a program that holds up under audit scrutiny.
Security Logging and Monitoring for SaaS: What SOC 2 and CMMC Both Require (And Why DevOps Owns It)
Security logging and monitoring is required by SOC 2 and CMMC — and it sits squarely at the intersection of compliance and DevOps. Here's what both frameworks require and what your engineering team needs to own.
Least Privilege Access: The Control That Shows Up in Every Framework and Fails in Most Audits
Least privilege access is required by SOC 2, CMMC, and ISO 27001 — and fails in most audits. Here's what the control actually requires across frameworks and where organizations consistently fall short.
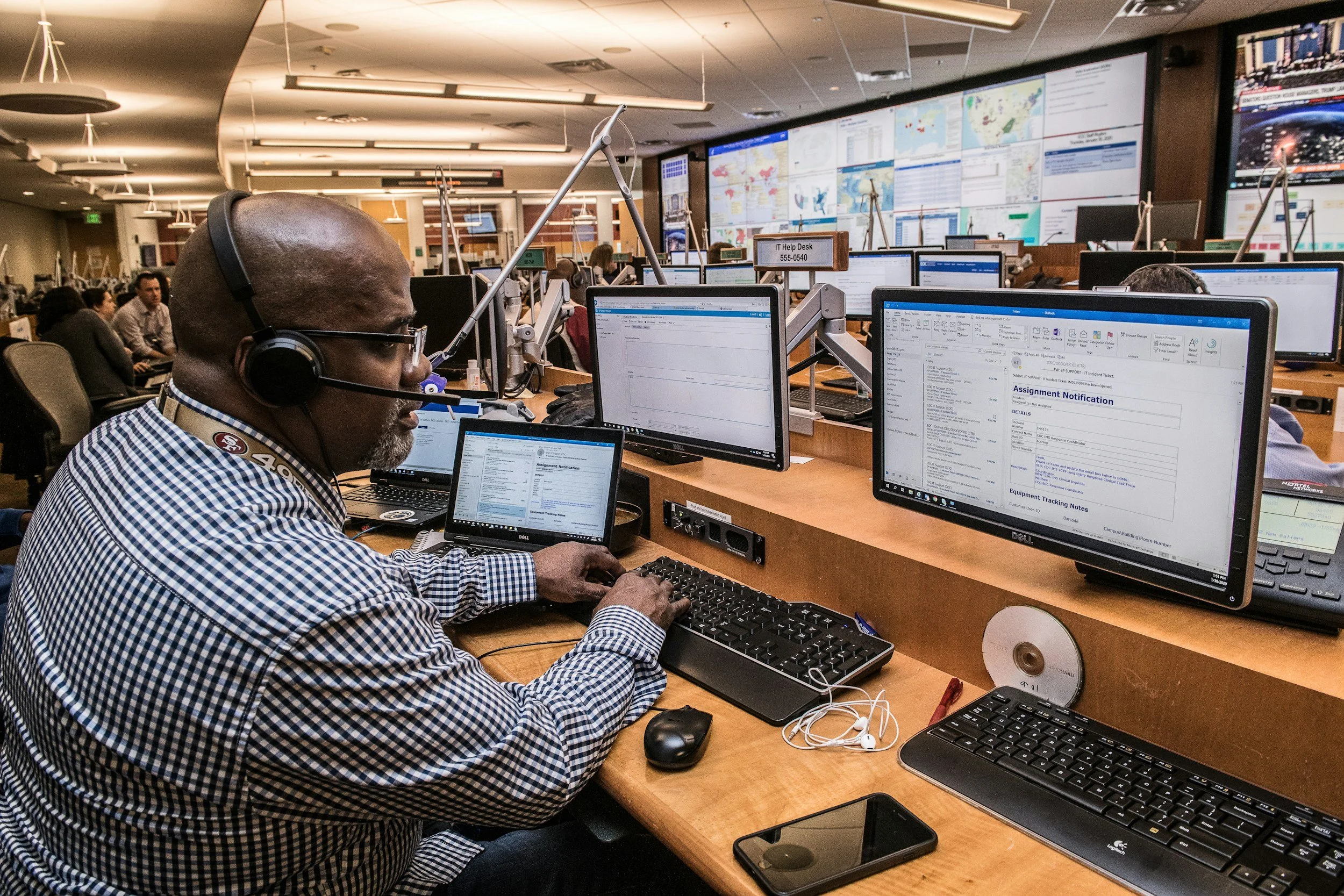
What a Tabletop Exercise Should Look Like, Include, and Why Auditors Care Whether You've Run One
Tabletop exercises are required by multiple compliance frameworks and consistently underprepared. Here's what a real tabletop should include, how to run one, and why auditors care whether you've done it.
What Is a SOC 2 System Description and Why Getting It Wrong Kills Your Audit
The SOC 2 system description is the foundation of your audit report — and one of the most misunderstood deliverables in the process. Here's what it needs to contain and where first-timers go wrong.
Steps to Achieve SOC 2 Compliance for Mid-Market SaaS: What You Actually Need
Wondering how to achieve SOC 2 compliance for your SaaS company without the 18-month nightmare? Tailored Compliance Solutions breaks down the real steps — clearly, in order, without the panic.
What Fractional Compliance Support Actually Looks Like: How TCS Engagements Work
What does working with a fractional compliance consultant actually look like? Tailored Compliance Solutions explains the engagement model, what to expect, and how it differs from hiring a big firm or going it alone.
Access Reviews for SOC 2: What They Are, How Often You Need Them, and What Auditors Actually Check
Access reviews are the most commonly failed SOC 2 control. Here's what they are, how often auditors expect them, and what "done right" actually looks like for SaaS companies.